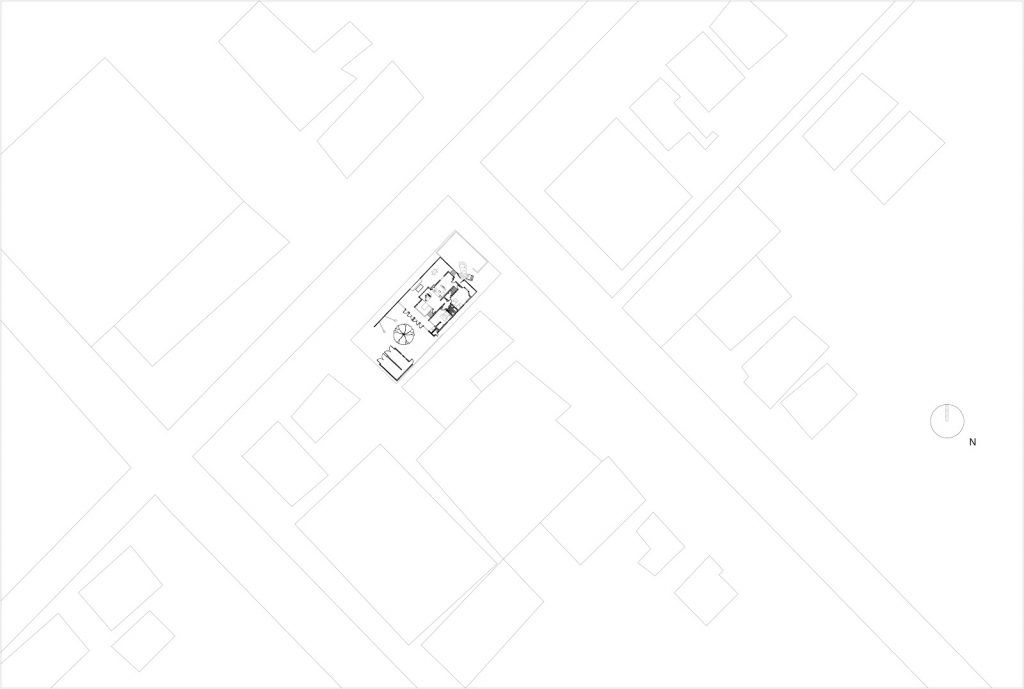
Gehry House
/
















The "detailed write-up" typically utilizes the suite, specifically Registry Explorer , to parse these hives.
: Standard locations like Downloads and Documents are the first places to check for user-created data or downloaded tools. 🛠️ Key Forensic Tools for Analysis Folder: 1
: Search for specific suspicious filenames (e.g., Changelog.txt ) or tools (e.g., mimikatz ) within the registry or common user folders. To track a user's recent activity, forensics experts
To track a user's recent activity, forensics experts analyze specific registry keys that store "shortcuts" to recently opened items. : These are found in the UsrClass
: A command-line tool often used in conjunction with batch files to quickly extract specific artifacts from registry hives.
: Use artifacts like Prefetch or ShimCache (AppCompatCache) to prove a file was not just present, but actually executed.
: These are found in the UsrClass.dat hive and track a user's browsing history within File Explorer. They store information about which folders were opened, their window size, and their view settings, even if the folder has since been deleted.