Using VerbAce-Pro
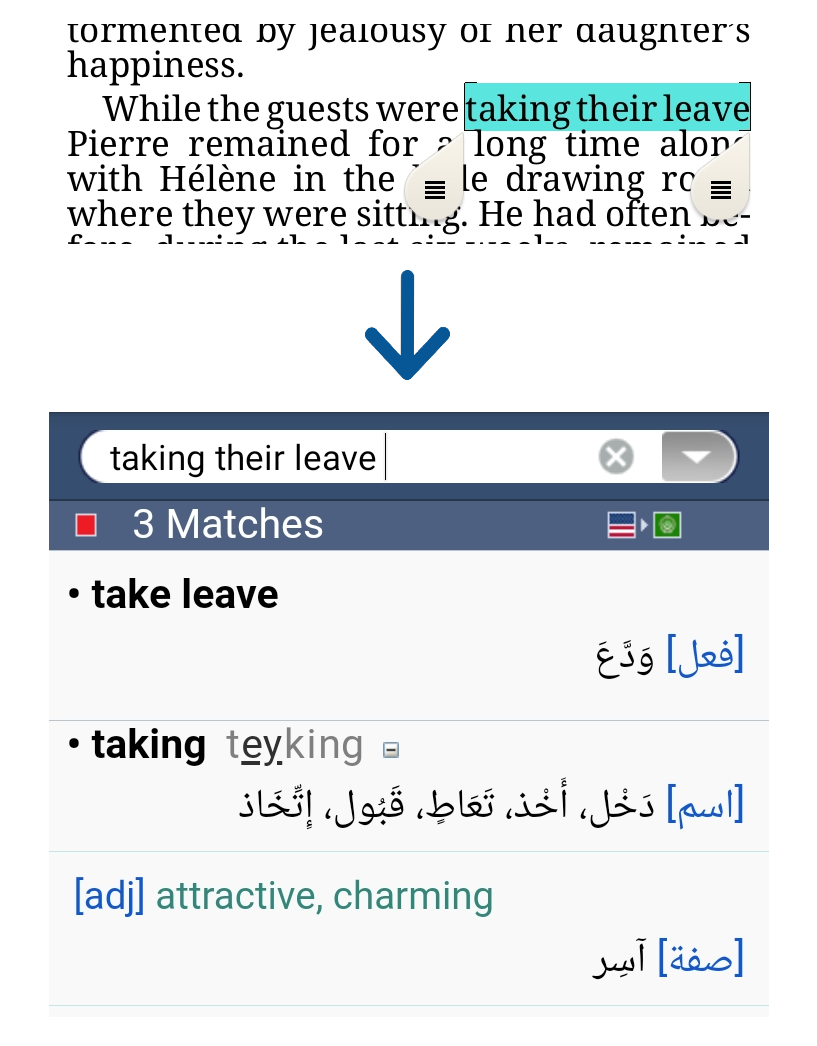
To use VerbAce-Pro just click on the word you want to translate, and the VerbAce-Pro results window will pop up with the trasnslation you need.
VerbAce-Pro captures and translates words and phrases from most Windows applications.
You can also pass the mouse over words and obtain quick translation via the Micro Window, or search for words by typing them in the term box.