Community discussions often echo these concerns, particularly regarding the deceptive nature of modern phishing.
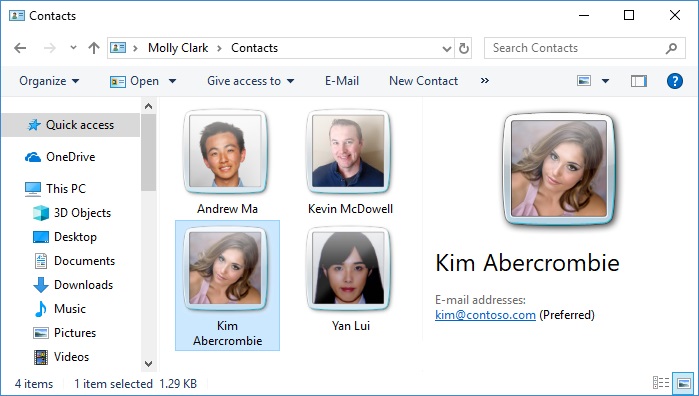
Be wary of apps asking for unnecessary access to your contacts, camera, or location. Human Insights on Mobile Security
Avoid "sideloading" apps or using unofficial marketplaces to reduce the risk of downloading malware.
This provides a critical second layer of defense even if a hacker manages to steal your password.
The article by AZMATH serves as a concise primer on mobile security, targeting everyday users who may not be aware of common digital vulnerabilities. While "AZMATH" appears to be a blog or author name associated with various cybersecurity professionals (such as Azmat Khan or Azmath Pasha ), the content typical of this title focuses on five primary threat vectors and their corresponding defenses. Common Attack Vectors Highlighted
5 Ways Hackers Can Attack Your Phone And Tips To Stay Safe Вђ“ Azmath ● < Limited >
Community discussions often echo these concerns, particularly regarding the deceptive nature of modern phishing.
Be wary of apps asking for unnecessary access to your contacts, camera, or location. Human Insights on Mobile Security
Avoid "sideloading" apps or using unofficial marketplaces to reduce the risk of downloading malware.
This provides a critical second layer of defense even if a hacker manages to steal your password.
The article by AZMATH serves as a concise primer on mobile security, targeting everyday users who may not be aware of common digital vulnerabilities. While "AZMATH" appears to be a blog or author name associated with various cybersecurity professionals (such as Azmat Khan or Azmath Pasha ), the content typical of this title focuses on five primary threat vectors and their corresponding defenses. Common Attack Vectors Highlighted